What is confidential Computing?
 Robert Young
Robert Young 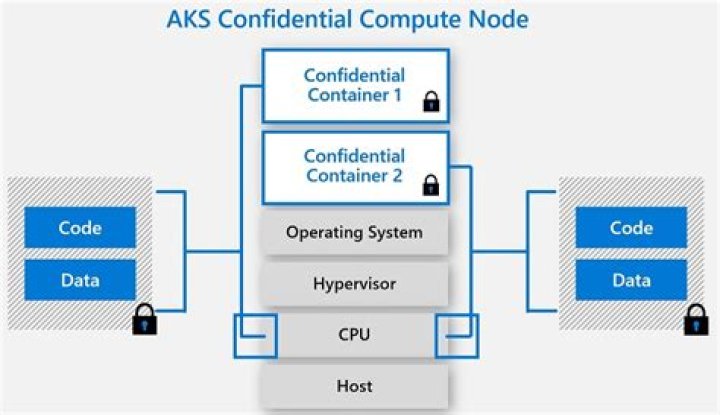
One significant approach is Confidential Computing: a technology that can isolate data and execution in a secure space on a system, which takes the concept of security to new levels.
Also asked, what is confidential compute?
Confidential Computing is a new technology that allows organizations to unlock the value of their most private data while keeping it more safe and secure. Organizations can now protect data and applications in use by running them within secure enclaves.
Subsequently, question is, what is Google confidential computing? Confidential Computing can provide a flexible, isolated, hardware-based trusted execution environment, allowing adopters to protect their data and sensitive code against malicious access and memory snooping while data is in use.
Consequently, what is confidential computing IBM?
Confidential computing protects sensitive data by performing computation in a hardware-based trusted execution environment (TEE). IBM Cloud® goes beyond confidential computing by protecting data across the entire compute lifecycle.
What is confidential computing Azure?
Azure confidential computing allows you to isolate your sensitive data while it's being processed in the cloud. Many industries use confidential computing to protect their data by using confidential computing to: Secure financial data. Protect patient information. Run machine learning processes on sensitive information.
Related Question Answers
What is confidentiality in cloud computing?
Data confidentiality. Data confidentiality is the process of protecting data from illegal access and disclosure from the outsourced server and unauthorized users. This is done by encrypting the data so that only the authorized users can decrypt it.Why do we need confidential computing?
Some of the benefits of confidential computing include: Protecting sensitive data while it is being processed: With confidential computing, data can be encrypted at rest and while in transit. This allows sensitive workloads to be managed by cloud assets because the data is protected while being processed.How can confidentiality be achieved?
Confidentiality – ensures that sensitive information are accessed only by an authorized person and kept away from those not authorized to possess them. It is implemented using security mechanisms such as usernames, passwords, access control lists (ACLs), and encryption.What is AMD sev?
In 2016, AMD introduced Secure Encrypted Virtualization (SEV), the first x86 technology designed to isolate virtual machines (VMs) from the hypervisor. Together with SEV, SEV-ES can reduce the attack surface of a VM by helping protect the confidentiality of data in memory.How confidentiality is used in cloud security model?
In cloud computing, user's data is stored on remote servers which may be operated by others and can be accessed through Internet connection. Confidentiality refers to the prevention of the unauthorized access of the data and hence making sure that only the user who has the permission can access the data.What is confidential VM?
A Confidential Virtual Machine (Confidential VM) is a type of N2D Compute Engine VM running on hosts based on the second generation of AMD Epyc processors, code-named "Rome." Using AMD Secure Encrypted Virtualization (SEV), Confidential VM features built-in optimization of both performance and security for enterprise-Why IBM believes confidential computing is the future of cloud security?
Confidential Computing is intriguing because it allows data to remain encrypted even as it's being processed and used in applications. Because the company hosting the data can't access it, this security standard could prevent hackers from grabbing unencrypted data when it moves to the application layer.What is IBM hyper Protect Crypto?
Overview. IBM Cloud® Hyper Protect Crypto Services is a dedicated key management service and Hardware Security Module (HSM)A physical appliance that provides on-demand encryption, key management, and key storage as a managed service. that provides you with the Keep Your Own Key capability for cloud data encryption.Is cloud computing the future?
Cloud computing is powerful and expansive and will continue to grow in the future and provide many benefits. Cloud computing is extremely cost-effective and companies can use it for their growth. The future of cloud computing is bright and will provide benefits to both the host and the customer.What is integrity in cloud computing?
Data integrity in the cloud system means preserving information integrity. The data should not be lost or modified by unauthorized users. Data integrity is the basis to provide cloud computing service such as SaaS, PaaS, and IaaS. Cloud computing providers are trusted to maintain data integrity and accuracy.What is compute power in cloud?
Cloud computing is the on-demand availability of computer system resources, especially data storage (cloud storage) and computing power, without direct active management by the user. Large clouds often have functions distributed over multiple locations, each location being a data center.What are hyper protect virtual servers?
IBM Hyper Protect Virtual Servers protect Linux® workloads on IBM Z® and LinuxONE throughout the application lifecycle – from build through to deploy and manage. Now you can be confident that applications and data are always private and protected from internal and external threats.What is Apple secure enclave?
The Secure Enclave is a dedicated secure subsystem integrated into Apple systems on chip (SoCs). The Secure Enclave is isolated from the main processor to provide an extra layer of security and is designed to keep sensitive user data secure even when the Application Processor kernel becomes compromised.How do I safeguard with hyper protective services?
Get started with Hyper Protect Crypto Services- Provision the service. Create an instance of the service to get started. Get started.
- Initialize the HSM. Initialize the crypto instance to protect key storage. Initialize the instance.
- Manage your keys. Learn more about keys and how to manage them. Manage keys.
How do private clouds work?
A private cloud uses virtualization technology to combine resources sourced from physical hardware into shared pools. This way, the cloud doesn't have to create environments by virtualizing resources one at a time from a bunch of different physical systems.How Azure is secure?
Automatic encryption.Everything sent within the Azure environment is automatically encrypted. The Azure network has automatic detection to prevent distributed denial-of-service (DDoS) attacks, similar to some of the largest services on the Internet, such as Xbox and Microsoft's Office 365.
What is an Azure enclave?
An enclave is a protected memory region that provides confidentiality for data and code execution. It is an instance of a Trusted Execution Environment (TEE) which is secured by hardware.What is open enclave SDK?
The Open Enclave SDK (OE SDK) is an open-source SDK that allows abstraction over different confidential computing-enabled hardware. The OE SDK can be used on top of Azure confidential computing virtual machines to create and run applications on top of enclaves.What is Intel SGX device and software?
Intel Software Guard Extensions (SGX) is a set of security-related instruction codes that are built into some modern Intel central processing units (CPUs). SGX is designed to be useful for implementing secure remote computation, secure web browsing, and digital rights management (DRM).What is azure attest?
Microsoft Azure AttestationVerify the identity and security posture of a platform before you interact with it. Azure Attestation receives evidence from the platform, validates it with security standards, evaluates it against configurable policies, and produces an attestation token for claims-based applications.