What is the first step in ISO IEC 27005 framework?
 Daniel Martin
Daniel Martin 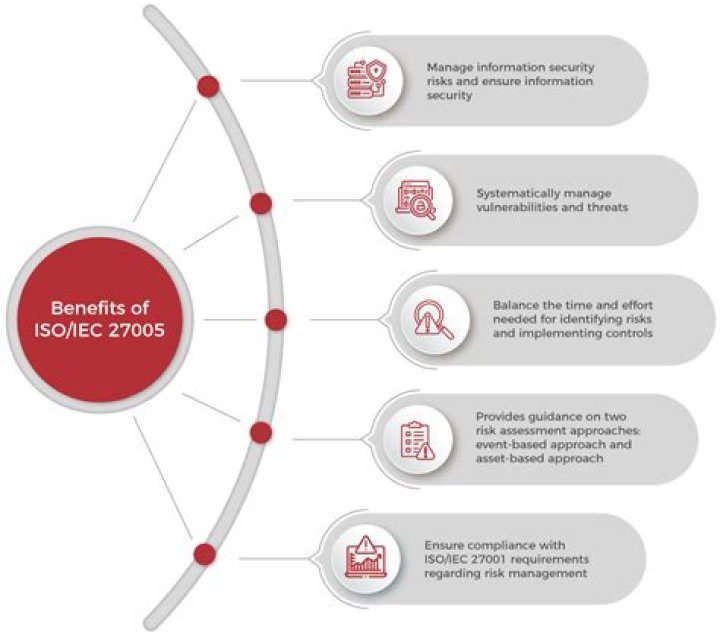
This step is the first step in ISO ISO/IEC 27005 framework. Most of the elementary activities are foreseen as the first sub process of Risk assessment according to NIST SP 800–30.
Consequently, what are the 7 steps of ISO IEC 27005 risk management process?
The ISO 27005 risk management process
- Context establishment.
- Risk assessment.
- Risk treatment.
- Risk acceptance.
- Risk acceptance.
- Risk monitoring and review:
Also, what are the 3 components in the risk assessment part of the ISO IEC 27005 2011 standard? 3 Terms and definitions
- 3.1. consequence.
- control. measure that is modifying risk (3.9)
- 3.3. event.
- external context. external environment in which the organization seeks to achieve its objectives.
- internal context.
- level of risk.
- likelihood.
- residual risk.
Similarly one may ask, what is the first step in the risk management process specified by the ISO 17779?
- Risk identification. The first step in the risk management process is to identify the risk.
- Risk analysis.
- Risk evaluation.
- Risk treatment.
- Monitor and review the risk.
What is the first step in ISO IEC 27001 2013?
Stage 1. Stage 1 of the initial certification audit focuses on the review of the design of the ISMS against the ISO 27001 standard as well as the organization's preparedness for Stage 2. The assessment is against the management system requirements, specifically clauses 4-10.
Related Question Answers
What are the steps involved in risk assessment and treatment?
Five Steps of the Risk Management Process- Step 1: Identify the Risk. The first step is to identify the risks that the business is exposed to in its operating environment.
- Step 2: Analyze the Risk.
- Step 3: Evaluate or Rank the Risk.
- Step 4: Treat the Risk.
- Step 5: Monitor and Review the Risk.
What is the purpose of ISO 27005?
ISO/IEC 27005 provides guidelines for the establishment of a systematic approach to Information Security risk management which is necessary to identify organizational needs regarding information security requirements and to create an effective information security management system.What are the steps to define the risk acceptance criteria and the criteria for performing information security risk assessments according to ISO 27001?
Risk assessments can be daunting, but we've simplified the ISO 27001 risk assessment process into seven steps:- Define your risk assessment methodology.
- Compile a list of your information assets.
- Identify threats and vulnerabilities.
- Evaluate risks.
- Mitigate the risks.
- Compile risk reports.
- Review, monitor and audit.
What is the difference between ISO 27001 and ISO 27005?
ISO 27001 requires you to demonstrate evidence of information security risk management, risk actions taken and how relevant controls from Annex A have been applied. ISO 27005 is applicable to all organizations, regardless of size or sector.What is the purpose of ISO 27005 and how does the standard relate to risk management in an enterprise network?
The basic objective in establishing the context of risk management is to know the risk appetite, or the level of risk that an organisation is willing to accept. ISO 27005 provides guidelines for establishing this context, which in turn determines the criteria for information security risk management.What is threat according to ISO 27005?
Regarding threats, ISO 27005 provides information about its type (e.g., physical damage, natural event, technical failure, etc.), examples (e.g., fire, dust, flood, defective software, etc.) and origin (e.g., intentional, accidental, etc.), but does not provide definitions, explanations or contextual examples.What is the sequence of risk management framework?
Risk identification, measurement, mitigation, reporting and monitoring, and governance are the six key pieces of an effective framework.What are the steps of security management?
I'll describe the steps involved in security management and discuss factors critical to the success of security management.- Step 1: Determine and evaluate IT assets.
- Step 2: Analyze risk.
- Step 3: Define security practices.
- Step 4: Implement security practices.
- Step 5: Monitor for violations and take corresponding actions.
What are the general steps for a security risk assessment?
The 4 steps of a successful security risk assessment model- Identification. Determine all critical assets of the technology infrastructure.
- Assessment. Administer an approach to assess the identified security risks for critical assets.
- Mitigation.
- Prevention.
What is the purpose of the ISO IEC 17799?
'ISO/IEC 17799:2005 establishes guidelines and general principles for initiating, implementing, maintaining, and improving information security management in an organization. The objectives outlined provide general guidance on the commonly accepted goals of information security management.What are the seven key steps in the risk assessment process?
7 steps of risk management are;- Establish the context,
- Identification,
- Assessment,
- Potential risk treatments,
- Create the plan,
- Implementation,
- Review and evaluation of the plan.
What is ISO risk management?
ISO 31000, Risk management – Guidelines, provides principles, a framework and a process for managing risk. Using ISO 31000 can help organizations increase the likelihood of achieving objectives, improve the identification of opportunities and threats and effectively allocate and use resources for risk treatment.What is correct with respect to the ISO IEC 27001 standard?
ISO/IEC 27001:2013 (also known as ISO27001) is the international standard for information security. Part of the ISO 27000 series of information security standards, ISO 27001 is a framework that helps organisations “establish, implement, operate, monitor, review, maintain and continually improve an ISMSâ€.What are the steps to preparing for and conducting an information security risk review?
How is an IT Risk Assessment Done?- Identify and catalog your information assets.
- Identify threats.
- Identify vulnerabilities.
- Analyze internal controls.
- Determine the likelihood that an incident will occur.
- Assess the impact a threat would have.
- Prioritize the risks to your information security.
- Design controls.
What is the risk management process?
The risk management process involves identifying, monitoring, and managing potential risks and their negative impacts on a business. Examples of potential risks include data loss, cyberattacks, security breaches, system failures, and natural disasters.What is octave risk assessment methodology?
OCTAVE is a flexible and self-directed risk assessment methodology. The team draws on the knowledge of many employees to define the current state of security, identify risks to critical assets, and set a security strategy. It can be tailored for most organizations.When was ISO 27005 created?
ISO/IEC 27005:2011 is applicable to all types of organizations (e.g. commercial enterprises, government agencies, non-profit organizations) which intend to manage risks that could compromise the organization's information security.What is the NIST Risk Management Framework?
The NIST Risk Management Framework (RMF) provides a comprehensive, flexible, repeatable, and measurable 7-step process that any organization can use to manage information security and privacy risk for organizations and systems and links to a suite of NIST standards and guidelines to support implementation of riskWhat is the difference between ISO 27001 and ISO 31000?
In clause 6.1. 3, ISO 27001 notes that information security management in ISO 27001 is aligned with ISO 31000. Therefore, ISO 27001 does not say you need to implement risk assessment and treatment according to ISO 31000 – it only says that all the requirements from ISO 27001 are already compliant with ISO 31000.What is the purpose of risk management framework?
A risk management framework helps protect against potential losses of competitive advantage, business opportunities, and even legal risks.What is IRAM2?
IRAM2 is a unique methodology for assessing and treating information risk. It includes guidance for risk practitioners to implement the six-phase process, consisting of Scoping, Business Impact Assessment, Threat Profiling, Vulnerability Assessment, Risk Evaluation, and Risk Treatment.Are deliberately risk aligned meaning organizations are encouraged to assess the security risks to their information?
Introduction. The ISO27k standards are overtly risk-aligned, meaning that organizations are supposed to identify and assess risks to their information (which are called “information security risks†in the ISO27k standards) as a prelude to dealing with (“treatingâ€) them in various ways.How many steps is ISO 27001?
Implementing an Information Security Management System aligned with ISO 27001. Following are the 10 key steps that one should milestone during implementation of ISO 27001: Define the Scope of Information Security Management System.What are the steps of implementing ISO 27001 for an organization?
ISO 27001 checklist: a step-by-step guide to implementation- Step 1: Assemble an implementation team.
- Step 2: Develop the implementation plan.
- Step 3: Initiate the ISMS.
- Step 4: Define the ISMS scope.
- Step 5: Identify your security baseline.
- Step 6: Establish a risk management process.
- Step 7: Implement a risk treatment plan.
What are the stages of isms phases?
The five stages of a successful ISO 27001 audit- Scoping and pre-audit survey. You must conduct a risk-based assessment to determine the focus of the audit, and to identify which areas are out of scope.
- Planning and preparation.
- Fieldwork.
- Analysis.
- Reporting.
What is the difference between SOC 2 and ISO 27001?
Differences: The main difference between SOC 2 and ISO27001 is that SOC 2 is focused mostly on proving the security controls that protect customer data have been implemented, whereas ISO 27001 also wants you to prove you have an operational Information Security Management System (ISMS) in place to manage your InfoSecWhat are the 114 controls of ISO 27001?
ISO 27001 controls list: the 14 control sets of Annex A- 5 – Information security policies (2 controls)
- 6 – Organisation of information security (7 controls)
- 7 – Human resource security (6 controls)
- 8 – Asset management (10 controls)
- 9 – Access control (14 controls)
- 10 – Cryptography (2 controls)
Which of the following are the steps in ISMS management framework?
Implementation Phases- Define an ISMS policy.
- Define the scope of the ISMS.
- Perform a security risk assessment.
- Manage the identified risk.
- Select controls to be implemented and applied.
- Prepare an SOA.
What are the 14 domains of ISO 27001?
The 14 domains of ISO 27001 are –| Information security policies | Organisation of information security |
|---|---|
| Human resource security | Asset management |
| Access control | Cryptography |
| Physical and environmental security | Operations security |
| Operations security | System acquisition, development and maintenance |
How do I get ISO IEC 27001?
How to get certified to ISO/IEC 27001- Gap analysis. This is an optional pre-assessment service where we take a closer look at your existing information security management system and compare it with ISO/IEC 27001 requirements.
- Formal assessment. This happens in two stages.
- Certification and beyond.
What are ISO 27001 requirements?
What are the ISO 27001 requirements?- Scope of the Information Security Management System.
- Information security policy and objectives.
- Risk assessment and risk treatment methodology.
- Statement of Applicability.
- Risk Treatment Plan.
- Risk assessment and risk treatment report.
- Definition of security roles and responsibilities.